Category: Crypto News
An Estate Planners Guide to Cryptocurrency – Handling Your Clients Cryptocurrency
Introduction
One of the most frequent emails we receive here at BePepared is “Help! My client is talking about cryptocurrency, and it all sounds like gibberish to me!”.
Have you found yourself in the same boat? If so – relax. Grab yourself a coffee, sit back and read on.
In this article, I’m going to break down for you in simple, easy-to-understand terms, exactly what the Blockchain is and how it works, how Cryptocurrency and NFTs function, and everything that you need to know to begin helping your clients manage their digital estate today.
The Beginning – Blockchain
The “Blockchain” is the technology upon which Cryptocurrency, NFTs and other ‘crypto’ applications are built – and so our explanation necessarily begins with understanding what the Blockchain is and how it works.
Insight #1 – At its core, a blockchain is a type of distributed database.
A database is a place where computers electronically organise and store information. Visually, a database looks somewhat like an excel spreadsheet, with rows and columns used to organise and store theinformation.
Now normally, a database exists on its own – and if it breaks, your data is gone. However, a Blockchain is a type of distributed database. This means that there are multiple, identical copies of the same database distributed across many different locations.
As a result, if one database broke for some reason, your computer would simply connect to another.
Insight #2 – Blockchains store data in blocks not tables

As we mentioned above, a standard database stores data in excel spreadsheets called ‘tables’. They have rows, and columns.
For example, a database of people’s names would have columns with ‘First Name’ and ‘Last Name’, and then each row would be a new person, with their first name and last name.
By contrast, a blockchain stores data in blocks.
What is a block?

A block is a record of information that contains 3 key things:
- The data it is storing
- The Hash for this block
- The Hash for the previous block
But what is a Hash?
‘Hashing’ is a cryptographic process where, by performing complex maths on some data, you can calculate its ‘fingerprint’.
I use the term ‘fingerprint’ because that is the function a hash ultimately performs, although, in reality, a hash looks like this: 34160e9836ba81b00081e2bbd6e2105a46a9525a
The above hash is what you get when you hash the phrase “Giant Red Banana”. Why not try it yourself here: Try Hashing
The computer takes the data (in this case the words you type in) and performs a hashing algorithm to create the above string of numbers and letters.
There are two key points to know about a Hash:
- It can’t be reverted to the original message. That is, there is no way to take “34160e9836ba81b00081e2bbd6e2105a46a9525a” and turn it back into “Giant Red Banana”; and
- If the data is changed even minutely (perhaps to “Giant Red Bananas”) – you will get a completely different hash.
I call a ‘hash’ a fingerprint because its ultimate function is to uniquely identify a piece of information, in the same way that our fingerprints uniquely identify us.
Insight – #3 – We chain these blocks together, to create a “Blockchain”
By chaining these blocks of data together, we get a Blockchain.
How does this work?
Each block in the chain contains the hash of the previous block.
As you’ll remember from our Hashes section – these are like a fingerprint, and are totally unique to the data it represents.
This means if someone went into the blockchain and tried to edit a previous block, it would immediately invalidate all the blocks after that block.
This is where the principle of immutability comes from. Once a block is added to the chain, it can’t be undone. It’s irreversible.
What would happen if someone did try to change a Blockchain?
In blockchains, the database works upon consensus.
So this edited Blockchain will be compared against all the other databases around the world- and if it doesn’t match the majority, it will be rejected and replaced with the correct information.
Because there are so many copies of the database, you would have to change 51% of the databases around the world simultaneously in order to alter the timeline. A feat that is for all practical purposes – impossible.
And this is how a Blockchain operates!
It’s a distributed database, that stores data in blocks (not tables), that are chained together to create an irreversible timeline.
Cryptocurrency
Now that we understand how a Blockchain works, we can begin to look at the technologies built on top of it – the most famous of which is Cryptocurrency.
Cryptocurrency is a digital currency that uses a Blockchain as its database. This allows it to maintain a distributed, immutable ledger.
So at a normal bank, the bank can see your bank balance, edit your balance, freeze your access to funds, and even also lose your money if they have a critical database crash.
With Cryptocurrency, a ‘wallet address’ has $10. No one can see whose wallet it is, no one can edit how much money you have, no one can freeze your money, and it would be very difficult for that many databases to all crash (at last count, there were ~70 million).
This is where the concept of Cryptocurrency being ‘decentralised’ comes into play – as there’s no governing authority controlling the ledger.
Exchanges
Your clients purchase their cryptocurrency on exchanges (similar to purchasing stock on a stock exchange) and then they can use those coins to purchase items or transfer money to other people.
Popular cryptocurrency exchanges include:
NFTs
Now “non-fungible tokens” or “NFTs” also operate on Blockchains.
The ‘non-fungible’ label means that, unlike Bitcoin where each coin is the same and can be exchanged interchangeably – an NFT is unique and each token holds unique values.
Famous examples of NFTs include:
Now, one of the most common misconceptions about an NFT, is that an NFT is a piece of artwork or a digital asset itself.
In actuality, an NFT is a form of providence. It’s a way of proving ownership of a digital item by using Blockchain technology – and most commonly, the item you own isn’t stored in the block itself, but linked to from the block.
In this case, the data the block contains is usually the asset hash (the thing that’s owned), the metadata or information about the item including a link to the item, and the providence and history of ownership.
Your clients purchase NFTs through marketplaces, such as OpenSea.
Storage & Wallets
Both Cryptocurrency and NFTs are stored in wallets.
Cryptocurrency wallets operate using public and private encryption keys.
Without getting too deep into the cryptography itself, the general principle is that data encrypted with the public key (called ‘public’ because any member of the ‘public’ can use it), can only be decrypted by the private key.
Another way to think about it is that the public key functions as your ‘account number’. You can give this ‘number’ to people, and using it, they can transfer you money or NFTs.
Using your private key, you can ‘log in’ to your wallet and use your money.
The actual wallets themselves also use cryptography to securely store the private key which functions as the ‘password’ to get the cryptocurrency or NFTs.
If your clients have Cryptocurrency or NFTs, they will be stored in a wallet. Wallets can come in many shapes and sizes, but the main wallets are your clients are likely to own include:
- Cold Wallets – A ‘cold wallet’ is any wallet that is completely disconnected from the internet. This prevents your wallet from being hacked, but it’s also a hassle to actually use any of your coins. A classic example of this is a paper wallet. A paper wallet is quite literally a piece of paper that has the key for your cryto wallet. There are other forms of wallets including metal wallets, but the risk all cold wallets face is someone finding/stealing it, and having access to all your assets.
- Hardware – a hardware wallet is a device, commonly similar to a USB stick, that allows you to access your wallet with a pin number when you need to use it. It has the advantage of being more secure than simply storing it on your computer, and safer than a piece of paper – but has its own risks. For instance, many hardware wallets will automatically delete your wallet if the wrong pin is entered too many times.
- Software – A software wallet is exactly what you’d expect – an application on your phone or your computer that will allow you to store, buy and sell cryptocurrency. Similarly, an exchange wallet is the default software wallet that an exchange keeps your cryptocurrency in before you transfer it elsewhere – much like a stock exchange keeps your money before you transfer it to your own account.
Handling Cryptocurrency and NFTs for clients
So your clients have Cryptocurrency, NFTs, and probably a heap of other digital assets too – such as passwords, domain names, websites, photo/videos and more – what should you do?
For a comprehensive analysis of different laws and solutions relating to digital assets, please see our Estate Planners Guide to Digital Assets
However, when handling Digital Assets for clients, you have 3 core requirements for any solution you deploy:
- The data must be secure
- The data must be easy to update and change when needed
- It must only be visible post death – not before.
What NOT to do:
- Use Google Sheets
- Use journals/envelopes
- Use Password Managers
Best Non-Paid Solution

The best non-paid solution for digital assets we’ve seen looks something like this.
- Your client creates an encrypted file on their computer, and puts all their important digital assets inside
- They store this encrypted file on their cloud storage (e.g. Dropbox or Google Drive) and share it with their Estate Lawyer
- The client separately provides their executor the access code to this encrypted file, or stores it in a safe deposit box.
- Upon death, the lawyer can share the encrypted file to the executor, who is now able to unlock the file and receive the documents
Important notes:
- If code is lost, the clients beneficiary can never access (fire, water, UV, theft)
- The client will have to update data from their computer.
- This requires the cloud service subscription to remain active and paid for.
- Some cloud platforms ‘expire’ their sharing links (e.g. iCloud), so clients may need to re-share every few months
- You (the estate planner) represent the primary risk in this situation, as you hold all the data
- If something happens to the estate planner, or they lose digital access to the encrypted file – all the data is lost
- The executor would technically be able to access the data before death if they got access to the clients or lawyers computer
Best Paid Solution
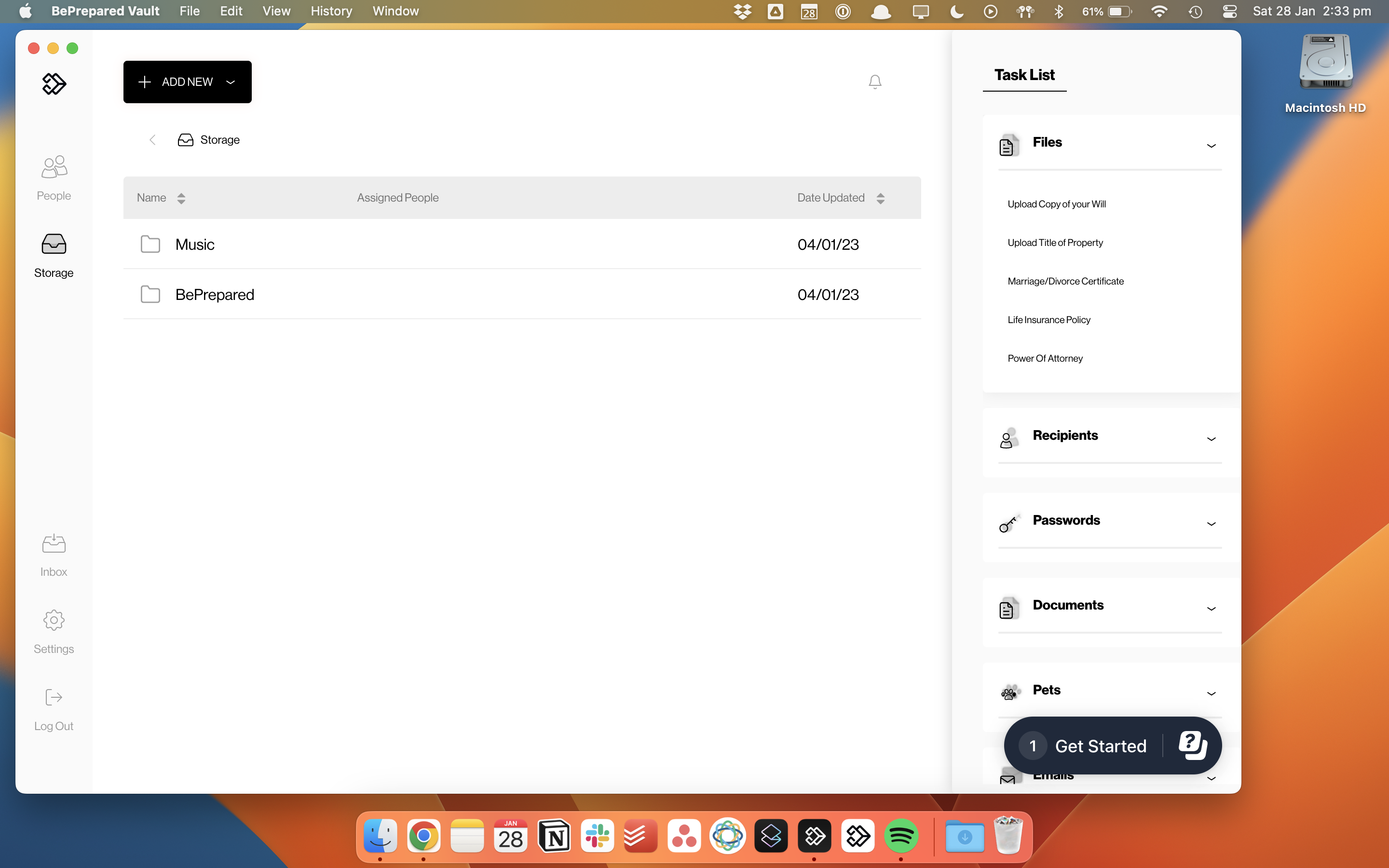
We won’t beat around the bush here – our platform was designed to handle this problem and we do it well. All our data is encrypted with military-grade security, and our platform is physical damage and theft proof. We have a rigorous death verification process to ensure data is only released post-mortem, and we’re easy for your clients’ to update from anywhere – Browser, Mobile or Computer. We allow your clients to choose who receives what data, and let all their advisors collaborate with them too, placing legal and financial documents in the vault on their behalf. If you’d like to know more, we recommend watching one of our online demos.
This article was submitted to be published by BePrepared as part of their advertising agreement with Today’s Wills and Probate. The views expressed in this article are those of the submitter and not those of Today’s Wills and Probate.
Written by : Editorial team of BIPNs
Main team of content of bipns.com. Any type of content should be approved by us.
Share this article: